Say Goodbye to loss of Crypto
Cypherock X1 is the World's safest hardware wallet with non-custodial inheritance
Security audited by Keylabs
The firm that found vulnerabilities in Ledger & Trezor hardware wallets

-
Varun Deshpande
Crypto Arbitrage Trader
Peter Schiff recently lost his entire $50 Bitcoin stash by not backing up his seed phrase.Cypherock hardware wallet ensures secure seed phrase backups — no single point of failure.
-

Kevin
Crypto Investor
One of the reasons I decided to go with Cypherock hardware Wallet is because of their security. I thought about trezor but Keylabs found flaws in their security.
-
Aaron Barboza
Crypto Trader
Be Your Own Bank with the Cypherock hardware Wallet.
-

Krishna Yogi
Crypto Investor
What Cypherock is doing is nothing short of a revolution in Bitcoin/ Crypto security! Rarely do we have a product that improves both on security and convenience!
-

Bitcoin Moses
Crypto Investor
I just got my Cypherock wallet in the mail. To hell with ledger. Seed phrase secure! Thank you to the Cypherock team. I see big things in the future for them.
USED BY HODLERS AT
Everything is hackable
Even your favorite wallets backups exchanges
But not with us
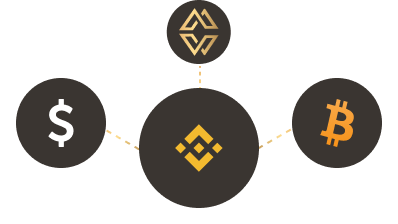
We don't centralise your keys like Wallets
We don't expose your keys like Backups
We don't store your keys like Exchanges
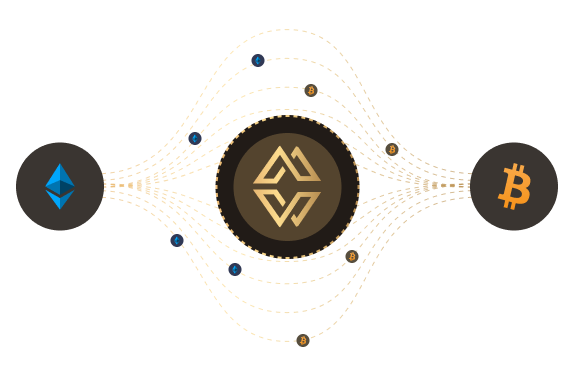
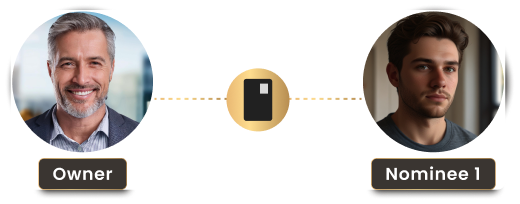
Cypherock X1 Hardware Wallet Decentralizes your private keys to Give you 10x More Security.

Splitting the Private Key

Storing Key Shards

Distributed for Maximum Security

Effortless Transactions

- No Seed phrase backups.
- No single point of failure.
- Just pure peace of mind.
-

Jane Doe
Crypto Consultant
Cypherock has redefined what the best hardware wallet should offer—top-notch security and effortless usability. It's a must-have for any crypto investor.
-

Rahul Mehta
Crypto Enthusiast
The Cypherock hardware wallet is a revolutionary solution for storing digital assets securely. Its unique design ensures peace of mind for crypto holders.
-

Maria Gonzalez
Crypto Educator
With Cypherock, I’ve found the perfect hardware wallet. The innovative seed phrase backup approach is truly ahead of its time.
-

Daniel Wu
NFT Collector
Cypherock is more than just a crypto wallet; it’s a comprehensive security solution. I trust it with my most valuable digital assets.
-

Emily Carter
Crypto Security Advisor
When it comes to protecting my cryptocurrency, Cypherock is the best hardware wallet available. Its cutting-edge features set it apart from the rest.
-

John Miller
Crypto Miner
Cypherock is the ultimate hardware wallet. Its decentralized key management gives me unmatched peace of mind for securing my crypto.
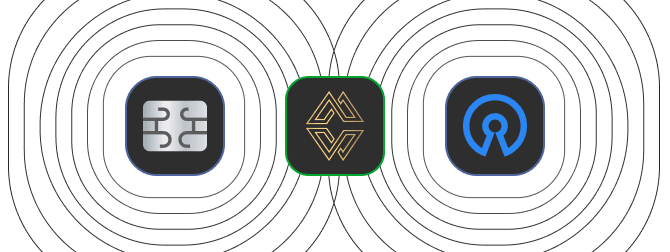
And that's not all
Cypherock X1 Hardware Wallet Gives you Features that
Others thought was not possible.
Without compromising security.

cySync App
Like an Expert

-
Om Malviya
Crypto Fund Manager
Just received my Cypherock wallet. Now I have a multi-sig hardware wallet where I don't need to store any seed-phrase. Can't wait to put this to work.
-

Smartytrader.crypto
Crypto Trader
Finally I got my Cypherock wallet yesterday and I have to say its build quality is so good. I didn't expect goodies like camera cover and Card covers (RFID COVER). You guys did such remarkable work Rohan Agarwal and Thomas Rishi for keeping users engaged in the community.
-

Crypto King
Social Media Influencer
New hardware wallet. I met the team in India at a conference 1 year ago and they brought their product to market!! Congrats team Cypherock, love the sleek design!
18000+ Digital Assets Supported
Backed by the best
Backed by the best




Buy the best hardware wallet today

Frequently asked questions
A hardware wallet is a physical device that securely stores your private keys offline, protecting your crypto from hacks and malware. Unlike software wallets, it keeps your keys isolated from the internet, reducing the risk of theft.
Yes! Hardware wallets provide superior security by keeping your private keys offline, protecting your assets from phishing attacks and hacks. They are a must-have for long-term crypto holders and anyone serious about securing their funds.
A hardware wallet protects your crypto from online threats like hacking, phishing, and malware. It ensures you have full control over your private keys, reducing the risk of losing funds due to exchange failures or cyberattacks.
A hardware wallet generates and stores your private keys securely offline. When making transactions, you connect the wallet to a device, verify the transaction on the hardware wallet, and then sign it securely before broadcasting it to the blockchain.
To transfer crypto, generate a receiving address from your hardware wallet and copy it. Then, send your funds from an exchange or software wallet to this address. Once confirmed on the blockchain, your assets are safely stored offline.
To withdraw crypto, connect your hardware wallet, select the asset you want to send, enter the recipient’s address, and confirm the transaction on the device. The wallet signs the transaction securely before broadcasting it to the blockchain.
Hardware wallets can be expensive and slightly less convenient than software wallets for frequent transactions. If lost or damaged without a backup, accessing funds may be difficult. However, solutions like Cypherock X1 eliminate seed phrase risks.
No, your crypto is stored on the blockchain, not the device. If you have a backup (like recovery seed or Cypherock X1’s key-sharing system), you can restore access. Without a backup, losing your private keys means losing your funds.